Please find below bitcoin wallet addresses being used by scammers. This list will be updated anytime I get new ones. 1CHVFbjh2KjUa6HhZEMcZK8sYHsA61L9y1 * NEW * 1JUPtgv3aY9EHNvwoAdFrt9ZCcgiUW48im * NEW * 17aB5wwDJ6EGdzzMgp3Y5deKCrqe7ga3qR 1FADcN5uSxtzV4E3zGCfQ4f3XzgxEPzT3M 1Pd7qACCUtM1zVXixbyxuJCXmDi4D1qMjn 1C2g3BixavU7Vupm1Atka6qErPZkhS18TY 1A28fiWUfQnqEMqoDmMf7KZcjSDY7mEjfs 1Abx3eY5pHFE1aC4AJLdU91qhHS5rzqP4E 19TkRECkDFuXq6E9zS7TxueE2RmZndJR8U 12mwSFYDyCWta8uMNxq52mENdi3nkjQGa5 1AMt6qukzLnSoT2eTv5Z9c2G24nQqNLUry 1PzZ3jX1zrGov2qyrMB8x3fKCrfxvTU2Tx 1JEvR3g6o6AbBZLWm9bvdVyeWk3yC8Rs8w 1DYfqwqz7Tq93Fau61YFXBAoogQv56FvJz 1AmP3aXEb7tv5M8gRGQfbAADBMmBPFhJNj 1LbbzFmNMMFMwsketCSzxAur6yinXBSiQQ 185kB82fakN7BCDpcS9tfzbDc8uytm5Wo 19gjxoZ2x8xzNC18FYtLxCL3FWRi15cP39 16RrKqp6gvepFSBMTcoVzdJZ1NSbA7PjZA 1BqMb5HKDj5xaTR65Psx1pfaDfzqWKPE65 1Mweet8rkufPJfge3fekvQLActb4wW5kNc 1EV3qSyz4XKoZAWvB1eVSYqHyqCNRdv9i7 15PjLxvFvVuUASkWLTReBDf1SAnGboiE3Q 17uRSEYKbco6kMrEc5aVCsCPAsFTVRPtsd 1MvogqA76t4o8Cya83SbPCGn52VRJsbiUV 17ychKgip2JpHf8uh5AJ6r5rXkmjSnQWaZ 15J3ZhZ6q6n2146Gdk5ncjqWaN84rNtvMd 1EfCwNrGgGbNAn4bKUX7XydSzFu4RHheC4 19U1xBf2UZeLfPkVh1Gu3WGHheYCzjsVxs 1GmtfRMFdctbJmhNZMgNNEeB7x1L8oKido 1MXEc4DhfxiTQgqcbajePjrEdtv6Ut46UT 1L1VmEatFZZSdU2DYD3JnS9RtpzXdPGmLZ 1HTAhiza95JocaB3ZtXrv5qmGPkjpBECNa 1N1AvndRxpo3dfKwaMTDmiy1Uaers6hZJk 1P28gw81epAv9RfjhaJikNjukboCrj8Lvn 1Fgiv3CQ15pkaMG4BzNzNiZGjy5NxaiLt5 Scam Advice If you receive an email resembling the examples provided below, we strongly advise reporting such instances to the Government's National Cyber Security Centre. Please forward the suspicious email to [email protected]. In the event that you suspect being a victim of fraud, we encourage you to submit a formal report either online or via telephone to Action Fraud. https://www.actionfraud.police.uk If the phishing attempt includes your password, it may be from past data breaches. If the email contains your actual password, change it immediately and consider enabling (2FA) Two-Factor Authentication. Check for potential compromises and receive future notifications at: haveibeenpwned.com If you're receiving what you believe to be scam texts, you can forward the text to 7726 along with the originating number from which you received the message. This information will be shared with all mobile operators who will block the number. If you receive a cold call from someone claiming to be from your bank, hang up immediately and call 159. This will connect you with your bank's fraud protection department. For more information on the 159 service, visit https://stopscamsuk.org.uk/.
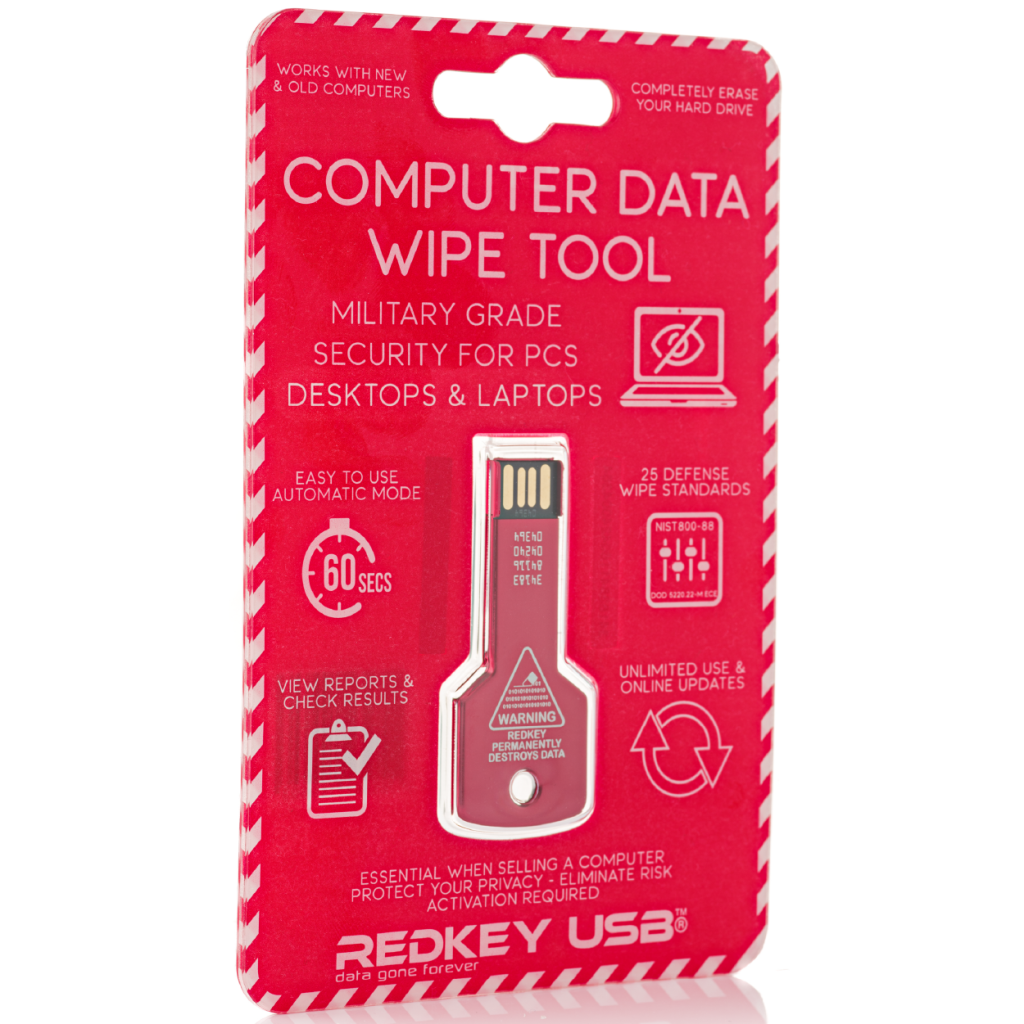
Redkey USB: Military Grade Security For PCs Desktops & Laptops; Data Gone Forever
What is Redkey USB? Redkey USB is the ultimate tool for erasing hard drives. It’s an easy-to-use, affordable solution that will help protect your privacy and ensure that no one can access your personal information. You don’t have to worry about anyone getting their hands on sensitive documents or pictures ever again! Key Selling Points One-time Purchase No Subscriptions No ongoing costs Certified (Scientifically proven) Unlimited use - Does not expire Redkey USB Specifications Easy to use Automatic Mode 25 Defense Wipe Standards View Reports & Check Results Unlimited Use & Online Updates (Does not expire) Technical...
ReleaseNotes; Update your product?
If you have recently completed product updates, it's important you let your customers know you have made improvements to your product. One of the most effective ways to share news of your updates and your product's story is to create and distribute release notes. In this blog post, we look at why release notes are important and how they can share news of your product updates. 1. Customer engagement Release notes are a powerful tool that can help engage new and existing users with your product. For example, if you have recently upgraded an area of your product...
11 ways to protect yourself from scam emails
Emails promising you all manner of riches in exchange for your bank details are the bane of every internet user's existence. But there are ways you can protect yourself from scam emails and avoid having to worry about con-artists emptying your bank account. 1) Don't be so quick to follow email links Many of these scammers try and entrap you by sending a link to your email which, if you click on it, could end up allowing the scammer to access your computer, locking it and preventing you from using it. 2) Look at the language used...

Grabify IP Logger & Url Shortener
The internet is not only the primary means of communication today; it also underpins many of the transactions and social exchanges we make. Everything takes place online, so having a means of tracking your engagement is crucial. Grabify is one of the most useful online tools to give you some insight into, and control over, the reach of your online presence. Read on to find out how. Introducing Grabify Grabify is an advanced and robust IP logger as well as a URL shortener. It divulges metadata and detailed statistical data about the links you provide...

Adult Website Email Scam: Don’t Give Bitcoin to Fraudsters
As we come to rely on technology more and more for our communication, it's natural that fraudsters, thieves, and swindlers are going to turn to those channels to ply their grim trade. Email, despite being old technology, is still one of the backbones of how we communicate digitally - and it's prime ground for scammers who will attempt to steal your identity, your money, and your confidential information. One, of many, types of scam emails allude to the use of adult sites. What do you need to know? What do the emails look like? Scam emails often...
How to remove viruses and malware from your PC
We all know how to keep our computers safe now, right? Install antivirus software and let that take care of you. Sit back, browse and download to your heart's content and watch the little digital warrior in the bottom right of your screen shoot down invaders with robotic precision. But what happens when you forget to update and something sneaks through? Or, perish the thought, you forgot to install the software in the first place? Now you're in a predicament. Surprisingly, not many people know how to cleanse their own computer after a successful virus or malware infection. ...
Sleep or Shut Down?
Sleep or shut down? When you’re finished with your computer at the end of the day, which option do you choose to put it to bed? Full shut down? Sleep? If it’s a laptop you’re working on, maybe you just close the lid and walk away. There are differences in each of these choices, and Dave’s Tech Support, offering computer repair services Holywood wide, are here to explain them. Full shut down A full shut down is exactly what it says. It’s like turning off the lights, and shutting down the hardware. The computer safely shuts down...
