Please find below bitcoin wallet addresses being used by scammers. This list will be updated anytime I get new ones. 17aB5wwDJ6EGdzzMgp3Y5deKCrqe7ga3qR 1FADcN5uSxtzV4E3zGCfQ4f3XzgxEPzT3M 1Pd7qACCUtM1zVXixbyxuJCXmDi4D1qMjn 1C2g3BixavU7Vupm1Atka6qErPZkhS18TY 1A28fiWUfQnqEMqoDmMf7KZcjSDY7mEjfs 1Abx3eY5pHFE1aC4AJLdU91qhHS5rzqP4E 19TkRECkDFuXq6E9zS7TxueE2RmZndJR8U 12mwSFYDyCWta8uMNxq52mENdi3nkjQGa5 1AMt6qukzLnSoT2eTv5Z9c2G24nQqNLUry 1PzZ3jX1zrGov2qyrMB8x3fKCrfxvTU2Tx 1JEvR3g6o6AbBZLWm9bvdVyeWk3yC8Rs8w 1DYfqwqz7Tq93Fau61YFXBAoogQv56FvJz 1AmP3aXEb7tv5M8gRGQfbAADBMmBPFhJNj 1LbbzFmNMMFMwsketCSzxAur6yinXBSiQQ 185kB82fakN7BCDpcS9tfzbDc8uytm5Wo 19gjxoZ2x8xzNC18FYtLxCL3FWRi15cP39 16RrKqp6gvepFSBMTcoVzdJZ1NSbA7PjZA 1BqMb5HKDj5xaTR65Psx1pfaDfzqWKPE65 1Mweet8rkufPJfge3fekvQLActb4wW5kNc 1EV3qSyz4XKoZAWvB1eVSYqHyqCNRdv9i7 15PjLxvFvVuUASkWLTReBDf1SAnGboiE3Q 17uRSEYKbco6kMrEc5aVCsCPAsFTVRPtsd 1MvogqA76t4o8Cya83SbPCGn52VRJsbiUV 17ychKgip2JpHf8uh5AJ6r5rXkmjSnQWaZ 15J3ZhZ6q6n2146Gdk5ncjqWaN84rNtvMd 1EfCwNrGgGbNAn4bKUX7XydSzFu4RHheC4 19U1xBf2UZeLfPkVh1Gu3WGHheYCzjsVxs 1GmtfRMFdctbJmhNZMgNNEeB7x1L8oKido 1MXEc4DhfxiTQgqcbajePjrEdtv6Ut46UT 1L1VmEatFZZSdU2DYD3JnS9RtpzXdPGmLZ 1HTAhiza95JocaB3ZtXrv5qmGPkjpBECNa 1N1AvndRxpo3dfKwaMTDmiy1Uaers6hZJk 1P28gw81epAv9RfjhaJikNjukboCrj8Lvn 1Fgiv3CQ15pkaMG4BzNzNiZGjy5NxaiLt5 Scam Advice If you receive an email resembling the examples provided below, we strongly advise reporting such instances to the Government's National Cyber Security Centre. Please forward the suspicious email to [email protected]. In the event that you suspect being a victim of fraud, we encourage you to submit a formal report either online or via telephone to Action Fraud. https://www.actionfraud.police.uk If the phishing attempt includes your password, it may be from past data breaches. If the email contains your actual password, change it immediately and consider enabling (2FA) Two-Factor Authentication. Check for potential compromises and receive future notifications at: haveibeenpwned.com If you're receiving what you believe to be scam texts, you can forward the text to 7726 along with the originating number from which you received the message. This information will be shared with all mobile operators who will block the number. If you receive a cold call from someone claiming to be from your bank, hang up immediately and call 159. This will connect you with your bank's fraud protection department. For more information on the 159 service, visit https://stopscamsuk.org.uk/.
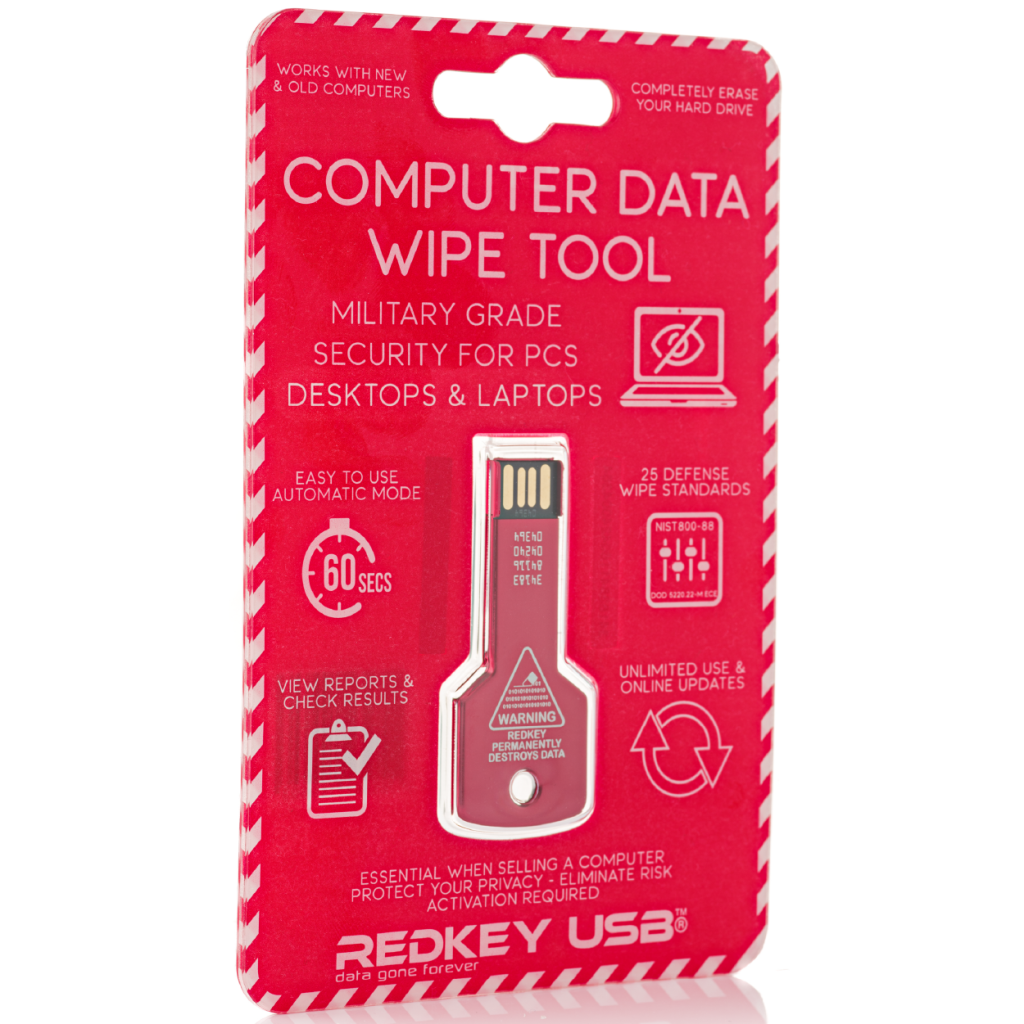
Redkey USB: Military Grade Security For PCs Desktops & Laptops; Data Gone Forever
What is Redkey USB? Redkey USB is the ultimate tool for erasing hard drives. It’s an easy-to-use, affordable solution that will help protect your privacy and ensure that no one can access your personal information. You don’t have to worry about anyone getting their hands on sensitive documents or pictures ever again! Key Selling Points One-time Purchase No Subscriptions No ongoing costs Certified (Scientifically proven) Unlimited use - Does not expire Redkey USB Specifications Easy to use Automatic Mode 25 Defense Wipe Standards View Reports & Check Results Unlimited Use & Online Updates (Does not expire) Technical...
Advantages & Disadvantages of Using SSD Solid State Drives
An SSD, which stands for solid state drive, is a device that uses integrated circuit assemblies to store data, often using flash memory. Solid state drives are commonly used in computers to replace traditional mechanical hard disks, offering a faster speed. Popular communication interfaces used with SSDs include NVMe and SATA. There are some advantages and disadvantages to using an SSD, which you should fully consider before upgrading to the device. To learn more about the main pros and cons of solid state drives, continue reading. Advantages Improved durability One great benefit of using an SSD is that...
hCaptcha - Stop more bots and start getting paid
While reCAPTCHA has been a staple for online businesses and services for what feels like decades, what once worked isn’t always the best approach for modern companies when it comes to maintaining privacy and security for users. hCaptcha is part of the new, user-friendly and practical generation of bot-blocking tools, building upon the Captcha legacy to create something thoroughly modern. Want to know more about what hCaptcha is, how it works, and how it measures up? Read on to find out more: What is hCaptcha? hCaptcha is, as the name suggests, a fully-fledged Captcha tool...
What is a Botnet?
The internet is a vital part of society now and central to our work and personal lives. This does not mean it is without its security concerns though. While you may have come across things like ransomware or phishing before, you might not have heard of a Botnet attack. Even if you have heard a friend mention Botnets, you might not be sure what it all means. Botnet 101 The first thing to know about Botnets is that they were actually designed for positive reasons and play a key role in how the internet functions. They provide the...
Benefits of disposable temporary phone numbers
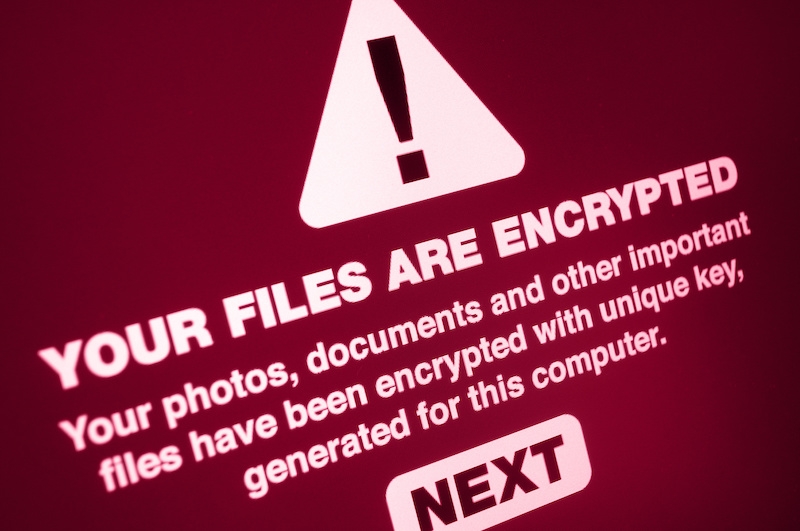
What is Ransomware?
Wondering what the idea behind the ransomware fuss is all about? You’ve probably heard the term at the office or read about it in some tech news article. Then suddenly, you get that pop-up on your computer screen warning you of a ransomware infection. Ransomware is a form of malicious software that locks and encrypts your computer or device data and then demands a ransom to restore access. Usually, the victim must pay the ransom within a set period or they risk losing access completely. Here’s a detailed report on ransomware, how to get them, types of ransomware, and how...

Grabify IP Logger & Url Shortener
The internet is not only the primary means of communication today; it also underpins many of the transactions and social exchanges we make. Everything takes place online, so having a means of tracking your engagement is crucial. Grabify is one of the most useful online tools to give you some insight into, and control over, the reach of your online presence. Read on to find out how. Introducing Grabify Grabify is an advanced and robust IP logger as well as a URL shortener. It divulges metadata and detailed statistical data about the links you provide...

Do you use public/shared phone chargers? You shouldn't, here's why
Many people quickly plug their USB cables in public charging ports to charge their phones when they run out of power while travelling or at work. They fail to consider the data privacy risks involved. Hackers can install technology, chips, and software that they use to infringe a person’s privacy. They can install malware that copies your data to their devices and sites. Charging ports are common in train stations, airports, bus stations, and schools, they help people to power their phones for continuous communication and access to the Internet. You need to take measures to prevent hackers from accessing...

Adult Website Email Scam: Don’t Give Bitcoin to Fraudsters
As we come to rely on technology more and more for our communication, it's natural that fraudsters, thieves, and swindlers are going to turn to those channels to ply their grim trade. Email, despite being old technology, is still one of the backbones of how we communicate digitally - and it's prime ground for scammers who will attempt to steal your identity, your money, and your confidential information. One, of many, types of scam emails allude to the use of adult sites. What do you need to know? What do the emails look like? Scam emails often...
